Successfully Implementing Information Security in Your Organization

Contents
Information Security in the Workplace: Fundamentals, Measures, and Strategy
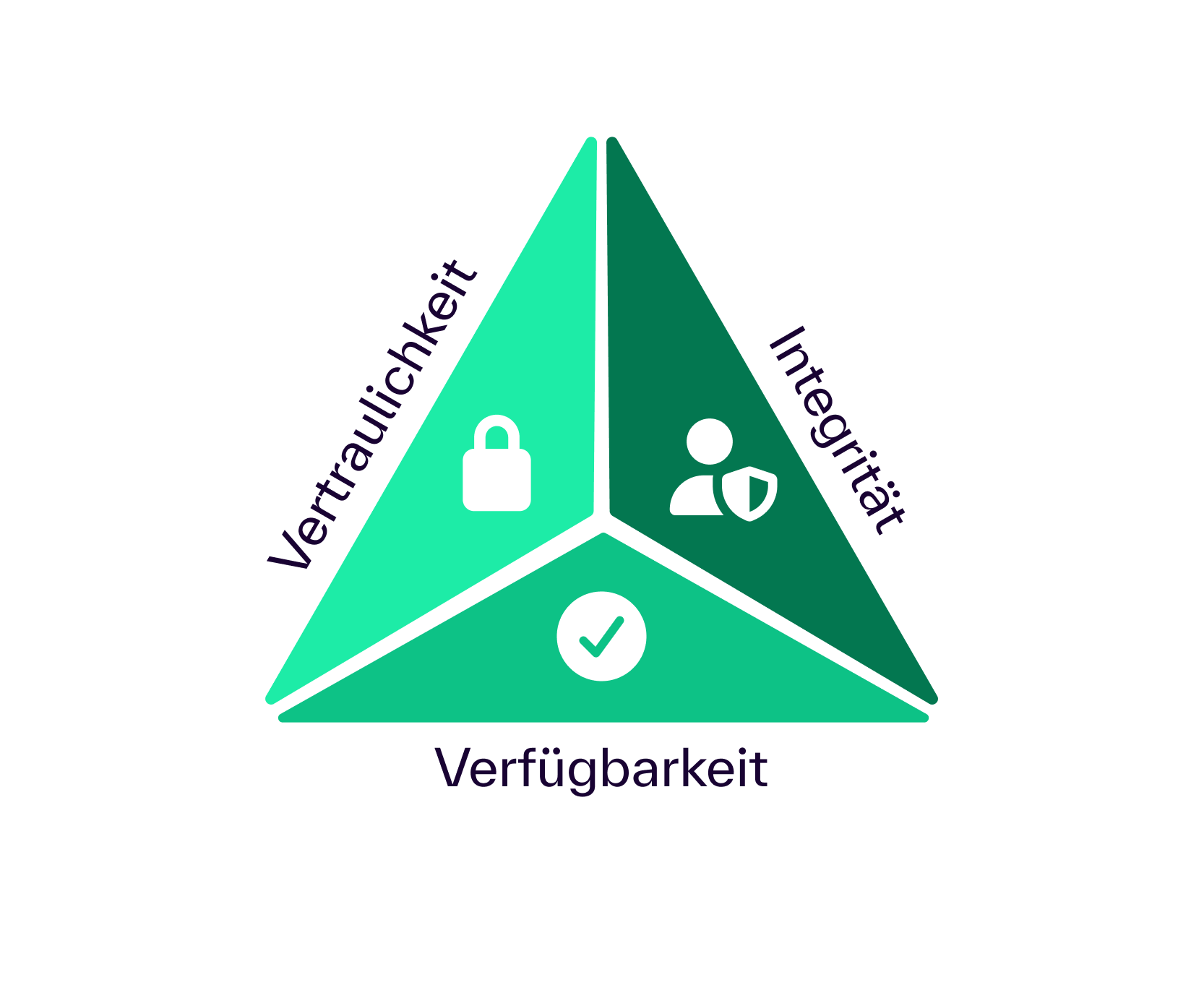
[DEFINITION][Information Security][Information security safeguards the confidentiality, integrity, and availability of your data and systems, ensuring that your business remains operational even in the event of attacks, errors, or outages.]
In this article, you’ll get a concise overview of the fundamentals and protection goals of information security, as well as the role of an ISMS as a foundation. You’ll then learn about key IT security measures for reducing attack surfaces and IT security processes for handling security incidents. Finally, you’ll learn how to secure people and the supply chain and establish an IT security strategy with a roadmap and key metrics within your organization.
Information Security: The Basics
- Information security is based on protection objectives: confidentiality, integrity, and availability form the foundation of all IT security measures.
- ISMS provides structure: An information security management system systematically manages roles, risks, and measures within the organization.
- Targeted reduction of attack surfaces: Identity protection, patch management, and secure architecture prevent common entry points for cyberattacks.
- Security processes ensure resilience: detection, response, and recovery limit the impact of security incidents and outages.
- Strategy makes security manageable: A roadmap, key performance indicators, and governance ensure that information security is permanently embedded in management.
What is information security?
In practical terms, information security means managing data, processes, and systems in such a way that confidentiality, integrity, and availability are maintained even in the face of attacks, errors, and failures. These three properties form the classic security objectives of information security and define what security in information technology actually means. Security becomes measurable because decisions are guided by clear objectives rather than individual tools. This is precisely where the foundations of IT security lie: first define the protection objective, then assess risks, and finally implement appropriate measures.
Information Security Objectives and the ISMS as a Foundation
These security objectives form the technical foundation of all IT security measures, as they translate the abstract concept of security into concrete requirements. The Federal Office for Information Security (BSI), Germany’s central authority for cybersecurity, describes confidentiality, integrity, and availability as the fundamental values of information security. Authenticity—that is, the verifiable authenticity of identities, systems, and communication partners—is often added to this list. As a result, IT security objectives serve as the basis for prioritization, auditability, and sustainable implementation within organizations.
- Confidentiality: Information is accessible only to authorized users, ensuring controlled access to company data. This is achieved through access controls, encryption, and data classification. As a result, the risk of misuse and data leakage is reduced, even in the event of a cyberattack.
- Integrity: Data and systems remain accurate and unchanged, except for authorized modifications. This requires change controls, digital signatures, logging, and structured access control policies. These measures reduce risks associated with tampering, Trojans, and user error.
- Availability: Systems, services, and information are available for use when needed. Redundancy, contingency plans, DDoS protection, and tested recovery from backups ensure continuous operation. This prevents security incidents from immediately leading to business disruption.
- Authentication: Identities, devices, and communication partners can be reliably verified. This is achieved through strong authentication, certificates, and privileged access controls. This helps you limit attacks on accounts, administrative systems, and critical applications.
An Information Security Management System (ISMS) translates these security objectives into roles, policies, risk decisions, and verifiable evidence. As a result, information security evolves from a one-off project into a continuous management process that clearly assigns responsibilities and is aligned with the organization’s requirements.
The international standard ISO/IEC 27001 outlines requirements for an ISMS and emphasizes the interconnection of people, policies, and technology in security management. In addition, the NIST Cybersecurity Framework 2.0 supports strategic management by defining Govern, Identify, Protect, Detect, Respond, and Recover as interconnected security functions.
In practice, security issues often arise not from a lack of technology, but from a failure to prioritize IT security management. Without clearly defined protection requirements and documented risk acceptance, budgets are often allocated to measures that are visible but ineffective, while real threats remain unaddressed. An ISMS provides structure here by defining which data is critical, which systems are considered crown jewels, and which risks are reduced, transferred, or deliberately accepted. This results in a robust IT security strategy rather than isolated IT security measures.
A current blind spot arises when generative AI is used without clear governance. Employees quickly transfer data to external applications, which can create security vulnerabilities and opportunities for misuse. In the absence of access controls, approval processes, and policies, such scenarios lead to security incidents regardless of existing firewalls or software solutions. An ISMS must therefore regulate which information is permitted to be transferred to which tools, who approves models, and how control is ensured in day-to-day operations, so that cybersecurity is maintained even with new technologies.
IT Security Measures: Reducing the Attack Surface and Securing the Architecture
The technical core of the IT security landscape lies in initial access—that is, an attacker’s first point of entry into systems or applications. This initial access is often gained through stolen credentials, exploitable vulnerabilities, or exposed edge devices within the IT infrastructure.
Studies show that the misuse of compromised login credentials remains one of the primary attack vectors, while the exploitation of security vulnerabilities is on the rise. This makes it clear that IT security measures must prioritize the protection of critical login points, remote access, VPN connections, and digital identities.
- Zero Trust as an architectural principle: Zero Trust describes a security model that does not implicitly trust network boundaries and replaces traditional perimeter security with continuous access controls. Every access request is verified based on identity, device, context, and risk, regardless of users location. This model is gaining importance for enterprise IT security as cloud services, hybrid work models, and partner access erode traditional security boundaries. Security is thus primarily achieved through controlled access to resources rather than through network isolation.
- Identity hardening as a core IT security solution: Digital identities are the most critical control point in modern IT security, as compromised accounts allow direct access to systems. Companies secure identities through multi-factor authentication, least-privilege models, separate admin identities, and privileged access management—that is, the targeted control of particularly critical access rights. In addition, session monitoring ensures that unusual activities are detected early on. Identity protection is thus one of the most effective elements of any IT security strategy.
- Vulnerability Management and System Hardening: Vulnerabilities constantly arise in software, applications, and IT infrastructures and must be systematically monitored. Vulnerability management describes the process of identifying, assessing, and addressing these security vulnerabilities within information technology. Key components include asset inventory, continuous vulnerability analysis, prioritization based on exposure and exploit availability, and virtual patching as a temporary protective measure. Reference frameworks such as the security controls of the National Institute of Standards and Technology (NIST), a U.S. agency for IT security standards, provide auditable guidelines for configuration, patch management, and logging.
- Application Security and Web Security: Web applications represent a distinct attack surface because they are publicly accessible, dynamic, and often dependent on third-party components. The international organization Open Web Application Security Project (OWASP) develops best practices and guidelines for secure web applications and, through the OWASP Top Ten, provides a structured overview of typical security risks. These include flawed access controls, insecure system configurations, and outdated software components, which can directly lead to security incidents. This model offers companies a practical introduction to structured application security and secure development.
- Data security as the core of information security: Protecting sensitive data is one of the central tasks of information security, as data breaches can result in financial losses and a loss of trust. Effective IT security measures include data classification, encryption, backup strategies, and data loss prevention—that is, mechanisms to prevent unintended data breaches. Rapid identification and containment of security incidents have been proven to reduce costs and operational impacts. Data security therefore combines technical controls with organizational security processes.
- Cloud Security and Shared Responsibility: In cloud and SaaS operations, security responsibility is shared between the provider and the organization, often referred to as the shared-responsibility model. Providers secure the infrastructure and platform, while configuration, identities, and data flows users the responsibility of users . Misconfigurations and dependencies within digital supply chains increase the attack surface and facilitate abuse. Effective IT security solutions therefore combine configuration monitoring, identity policies, logging, and supply chain controls, thereby providing comprehensive protection in hybrid IT infrastructures.
IT Security Processes for Handling Security Incidents
No protection is foolproof, which is why information security must kick in operationally as soon as an attack succeeds. The NIST Cybersecurity Framework 2.0, an internationally recognized framework for cybersecurity, describes this lifecycle through the phases of Detect, Respond, and Recover, and supplements it with Govern, Identify, and Protect as ongoing preparedness measures. For companies, this results in a clear management model: How quickly do you detect security incidents, how effectively do you stop attacks, and how swiftly do you restore systems? IT security processes translate these questions into measurable workflows rather than isolated security measures.
- Visibility and detection as a foundation: Effective incident response begins with transparency regarding events within the IT infrastructure. Without logging, alerting, and forensic analysis, attacks remain undetected for longer, increasing damage and risks. Studies show that rapid identification and containment of security incidents generate direct cost savings and are increasingly supported by automation. As a result, information security in a management context becomes a matter of measurable response times rather than mere tool implementation.
- Reporting channels and regulatory requirements: Reporting processes are now an integral part of an organization’s operational IT security and are not solely a compliance issue. The European NIS2 Directive defines a multi-tiered reporting framework with early warning within 24 hours, incident reporting after 72 hours, and a final report within one month. These requirements affect numerous critical sectors and underscore the importance of structured communication and escalation processes. Security incidents must therefore be technically detected, organizationally assessed, and reported to regulators.
- Ransomware Resilience and Recovery: Ransomware serves as a key stress test for security processes, as it targets availability and is often combined with data exfiltration. A resilient recovery process includes tested recovery procedures, verified integrity of backup copies prior to restoration, and coordinated communication measures. These capabilities reduce downtime and limit the economic impact of cyberattacks. Resilience is thus achieved not through prevention alone, but through reliable recovery capabilities.
- Protection against availability attacks: Attacks targeting the availability of digital services—particularly DDoS attacks—are among the most common types of incidents reported in European security briefings. Companies therefore need both preventive and reactive measures to ensure the stability of business-critical online services. Typical protective mechanisms include web application firewalls, content delivery networks, rate limiting, and coordinated emergency plans with providers. These measures ensure operational capability even under heavy load caused by targeted attacks.
- Learning cycle and continuous improvement: IT security processes only become effective through systematic follow-up on incidents and near-misses. The NIST Cybersecurity Framework describes profiles and maturity levels that provide transparency regarding the current state, target state, and progress of security efforts. This enables companies to prioritize measures and expand their security capabilities in a targeted manner. Information security thus becomes a continuous improvement process rather than a reactive one-off measure.
People and the supply chain as factors in information security
Information security is often viewed as a purely technical issue, even though human behavior plays a central role in security incidents. Analyses show that users are directly involved users many attack scenarios, for example through phishing, social engineering, operational errors, or the unintentional misuse of access credentials. Awareness, therefore, does not refer to a one-time training session, but rather to an ongoing security process that includes training, testing, and clear rules of conduct. Online security is thus not achieved through technology alone, but through secure decisions made in everyday work.
- Security Awareness and Human Risk Management: Employees interact with data, applications, and systems on a daily basis, thereby forming a critical security boundary within the IT infrastructure. Effective awareness programs combine training, phishing attack simulations, and transparent feedback to measurably improve security skills. Clear guidelines, simple reporting channels, and supportive security measures reduce operational errors and encourage responsible behavior. Human Risk Management transforms information security into an organizational capability rather than a purely technical protective measure.
- Generative AI Use and Shadow AI: The use of generative AI in everyday work enhances productivity and expands operational flexibility, but at the same time increases the risk of data leakage. Employees frequently transfer content to external platforms, which can result in confidential information being processed without proper oversight. Shadow AI refers to the use of unauthorized AI tools without governance, access controls, or policies, making it a significant information security concern. Companies need clear rules for data usage, tool approvals, and access controls to ensure cybersecurity even with new technologies.
- The supply chain and third parties as a security factor: Digital dependencies increase the attack surface, as partners, service providers, and software vendors gain direct or indirect access to systems and data. Security incidents within the supply chain can have repercussions across multiple organizations and enable attacks to scale. European situation analyses show the growing significance of such cyber dependencies, i.e., digital dependencies between companies. Information security within the company must therefore systematically account for partner access, integrations, and external services.
- Supplier Security as a Structured Process: Supplier Security refers to the systematic safeguarding of external service providers and technology partners within an IT security strategy. This includes security requirements in contracts, minimum standards for technical access, proof of patching and incident response capabilities, and coordinated runbooks for security incidents. Frameworks such as the CIS Controls, developed by the Center for Internet Security, provide prioritized protective measures against common cyberattacks and support implementation in cloud and hybrid environments. Supplier Security reduces risks not through one-off audits, but through permanently established security processes.
- Insider Risks and Access Control: Insider risks do not arise solely from malicious acts, but often from legitimate access combined with misconduct or changes in roles. Highly privileged accounts, in particular, can trigger security incidents with severe consequences, as they provide direct access to critical systems and corporate data. Prevention therefore relies on structured authorization models, separation of duties, monitoring of security-related activities, and the prompt revocation of privileges in the event of organizational changes. Access control thus becomes a central element of data security and overall IT security.
IT Security Strategy: Roadmap and Management of Information Security
An effective IT security strategy rarely fails because of its objectives, but rather due to a lack of prioritization and the failure to translate them into meaningful steps. The NIST Cybersecurity Framework 2.0 provides a structured model for this purpose, comparing the current state with the target state and defining maturity levels to prioritize measures based on risk. This makes information security predictable, budgetable, and directly translatable into management decisions. In this context, strategy means sequencing security measures according to the greatest risks rather than implementing them in isolation.
- Initial Phase with Minimum Viable Security: The first step is to establish fundamental security capabilities that address key entry points for cyberattacks. These include identity hardening, asset inventory, prioritized patching processes, and basic logging to provide visibility into security-related events. These measures significantly reduce risks associated with compromised credentials and unpatched vulnerabilities. Minimum Viable Security thus creates a robust foundation for further security processes.
- Stabilization phase with operational resilience: Once basic security measures are in place, the next step is to operationalize IT security processes to manage security incidents in a controlled manner. Key elements include incident response plans, regular drills, backup and recovery tests, and coordinated emergency procedures for availability attacks. Resilience here refers to the ability to quickly restore business operations despite attacks. This phase embeds security measures into day-to-day operations and minimizes the impact of security incidents.
- Scaling phase with structural safeguards: In the next step, security measures are standardized across the organization, supply chain, and technology. This includes structured supplier security, application security in accordance with OWASP guidelines, cloud security configuration, and governance for new technologies such as generative AI. The goal is to manage growing digital dependencies in a controlled manner and reduce persistent attack surfaces. Scaling thus means establishing information security as a company-wide capability.
The IT security report serves as a key management tool that provides transparency regarding this roadmap within the organization. Relevant metrics include, for example, MFA coverage, patch status of critical systems, remediation times for exposed vulnerabilities, time to detection and containment of security incidents, and recovery success following outages. In addition, metrics on third-party exposure enable an assessment of supply chain risks. This makes IT security within the company verifiable from a management perspective without getting bogged down in technical details.
Certification supports the strategic implementation of information security through structured documentation and prioritization. ISO/IEC 27001 outlines requirements for information security management systems and is internationally recognized as the benchmark for an effective ISMS. In addition, ISO/IEC 27002 provides specific best-practice controls for the operational implementation of security measures. Certification builds trust among stakeholders while simultaneously supporting internal governance and management processes.
For companies with EU operations, the NIS2 Directive is a key consideration in strategic planning, as reporting obligations and risk management constitute mandatory requirements. The directive sets clear deadlines for security notifications and covers numerous critical sectors within the European Union. The Federal Office for Information Security (BSI), Germany’s central cybersecurity authority, provides guidance and tools for this purpose, such as a NIS2 impact assessment. This allows governance requirements to be linked to operational information security at an early stage.
Building Information Security Strategically: Skills and Professional Development as Key Success Factors
Information security can only be fully effective when strategy, technology, and processes are supported by the appropriate skills within the organization. Employees, managers, and executives need structured knowledge of IT security, ISMS, cybersecurity, and regulatory requirements. Continuing education lays the foundation for correctly implementing security measures, professionally managing security incidents, and permanently embedding information security within management. Qualification thus becomes a central component of every IT security strategy.
Structured professional development programs help you build practical information security skills and confidently meet regulatory requirements. These include training on ISO/IEC 27001, auditor and implementer roles, CISO competencies, and AI management systems. These programs combine the fundamentals of IT security with operational implementation and strengthen skills in governance, risk management, and incident response. At the same time, certifications make it easier to demonstrate structured security expertise to stakeholders and partners.
If you’d like to systematically deepen your knowledge of information security and build your skills in a targeted way, you’ll find suitable training opportunities at:
https://www.haufe-akademie.de/skill-it/subcategories/informationssicherheit-28iso-29
The training courses available there will help you strategically shape information security within your organization, effectively implement security measures, and ensure a robust level of security over the long term.
In addition, our blog posts on IT-Grundschutz, cybersecurity, and cloud security provide in-depth insights into key areas of information security.


